Ultimate Guide to Enterprise Security Workforce Management Software
Managing global security operations while maintaining compliance, controlling costs, and ensuring comprehensive coverage requires more than basic workforce management tools. The stakes are higher when protecting large-scale operations across multiple locations, languages, and regulatory environments.
The right security workforce management platform can transform your operations from reactive to proactive, providing the centralized control and visibility enterprise security leaders need. After analyzing the top platforms available in 2025, we’ve identified the key features that matter most for enterprise security teams and how leading solutions measure up.
What Enterprise Security Teams Need Most
Enterprise security operations face unique challenges that distinguish them from standard workforce management needs:
- Scale and Complexity: Managing hundreds or thousands of security personnel across multiple sites, time zones, and jurisdictions requires sophisticated coordination capabilities.
- Regulatory Compliance: Enterprise security teams must navigate complex compliance requirements, from local regulations to industry standards like SOC 2, while maintaining detailed audit trails.
- Risk Management: Proactive threat assessment and incident response capabilities are essential for preventing security breaches before they occur.
- Integration Requirements: Modern security operations centers rely on multiple specialized tools. Your workforce management platform must integrate seamlessly with existing security infrastructure.
- Global Operations: Support for multiple languages, local regulations, and cultural differences while maintaining centralized oversight and standardized procedures.
Top Security Workforce Management Platforms for Enterprise
When it comes to managing security at enterprise scale, not all platforms are equipped to handle the complexity, global reach, and integration needs of large organizations. Here’s how the industry leaders compare:
Quick Comparison Table —
2025’s Top Platforms
 |
Belfry |
Connecteam |
24/7 Software |
GuardsPro |
Celayix |
OfficerReports |
|
Global Support |
Limited: Primarily focused on a single region; no multi-language or global compliance support. |
Basic: Some language support but lacks enterprise-level global compliance tools. |
Limited: Focused on venue management; not designed for global security operations. |
Limited: Lacks multi-language support and features for international compliance. |
Basic: Primarily a scheduling tool; lacks specific global security operation features. |
Limited: Primarily focused on a single region; no global scalability features. |
|
Proactive Risk Management |
Basic: Standard incident reporting but lacks proactive or analytical tools. |
Basic: General task and incident forms; not tailored for security risk assessment. |
Good: Strong incident management for venues but not for proactive enterprise-wide risk. |
Good: Offers incident and activity reporting but lacks advanced analytics. |
Minimal: Focus is on scheduling, not risk management or incident reporting. |
Good: Provides real-time reporting but lacks deep analytical capabilities. |
|
Automated Compliance |
Minimal: Lacks automated tools for ensuring compliance across multiple sites. |
Minimal: Lacks specific, automated compliance features for security operations. |
Basic: Some compliance tracking but not automated for enterprise-scale security. |
Basic: Manual reporting for compliance; lacks automated audit trails. |
Minimal: No dedicated features for automated security compliance or audit trails. |
Basic: Offers report tracking but no automated compliance enforcement tools. |
|
Data Ownership |
Limited: Data access is restricted to the platform’s ecosystem; no full ownership. |
Limited: Data is managed within the platform with limited export options. |
Limited: Data is tied to the platform, with minimal options for external control. |
Limited: Data access is platform-dependent; lacks full user ownership. |
Limited: Data is managed within the platform with no clear data ownership policies. |
Limited: Data is accessible via the platform but lacks full external control. |
|
Integration/API Capabilities |
Minimal: Lacks an open API for integration into a unified security operations center. |
Basic: Some integrations available (e.g., payroll) but not for security-specific systems. |
Basic: Limited API connectivity, not designed for broad security system integration. |
Minimal: No significant integration capabilities with other security technologies. |
Basic: Offers payroll and HR integrations but lacks a security-focused API. |
Minimal: No open API for connecting to a broader security technology stack. |
|
Enterprise Suitability |
Not Suitable: Designed for small to mid-sized security guard companies. |
Not Suitable: A general workforce tool, not specialized for enterprise security needs. |
Not Suitable: Niche focus on venue/event management, not enterprise security. |
Not Suitable: Geared towards smaller security firms and patrol management. |
Not Suitable: Primarily a scheduling solution, lacking security-specific features. |
Not Suitable: Designed for small to mid-sized guard companies, not enterprise scale. |
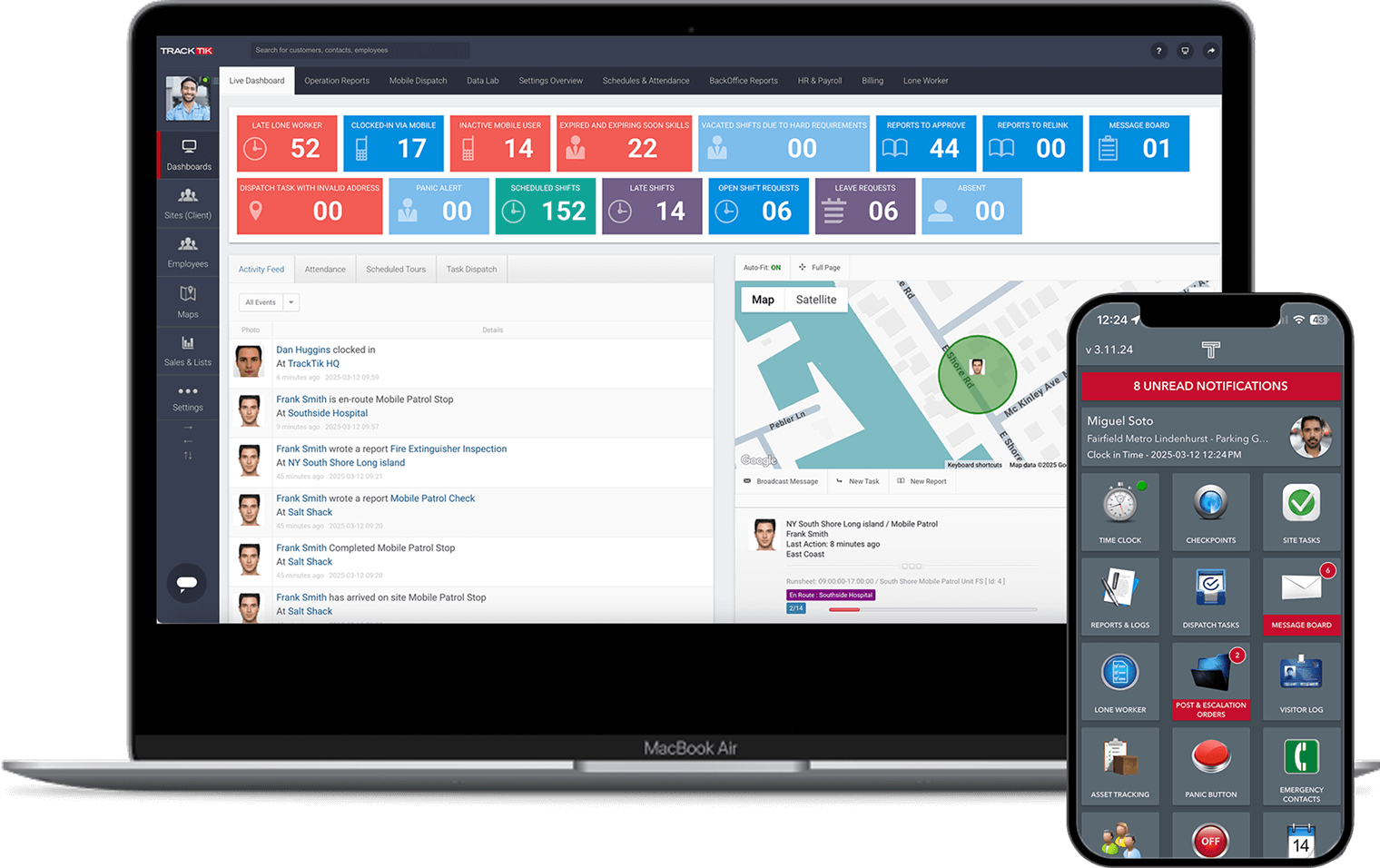
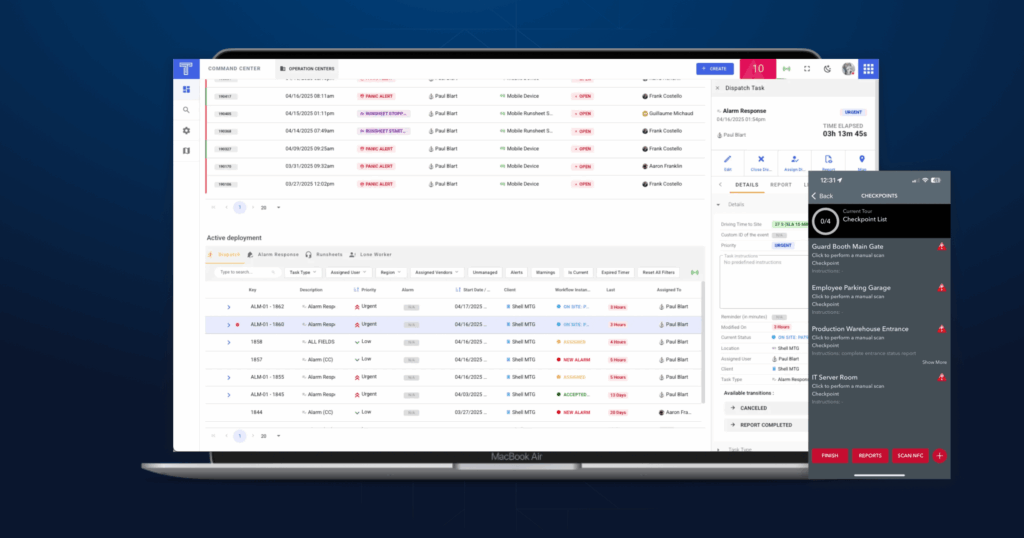
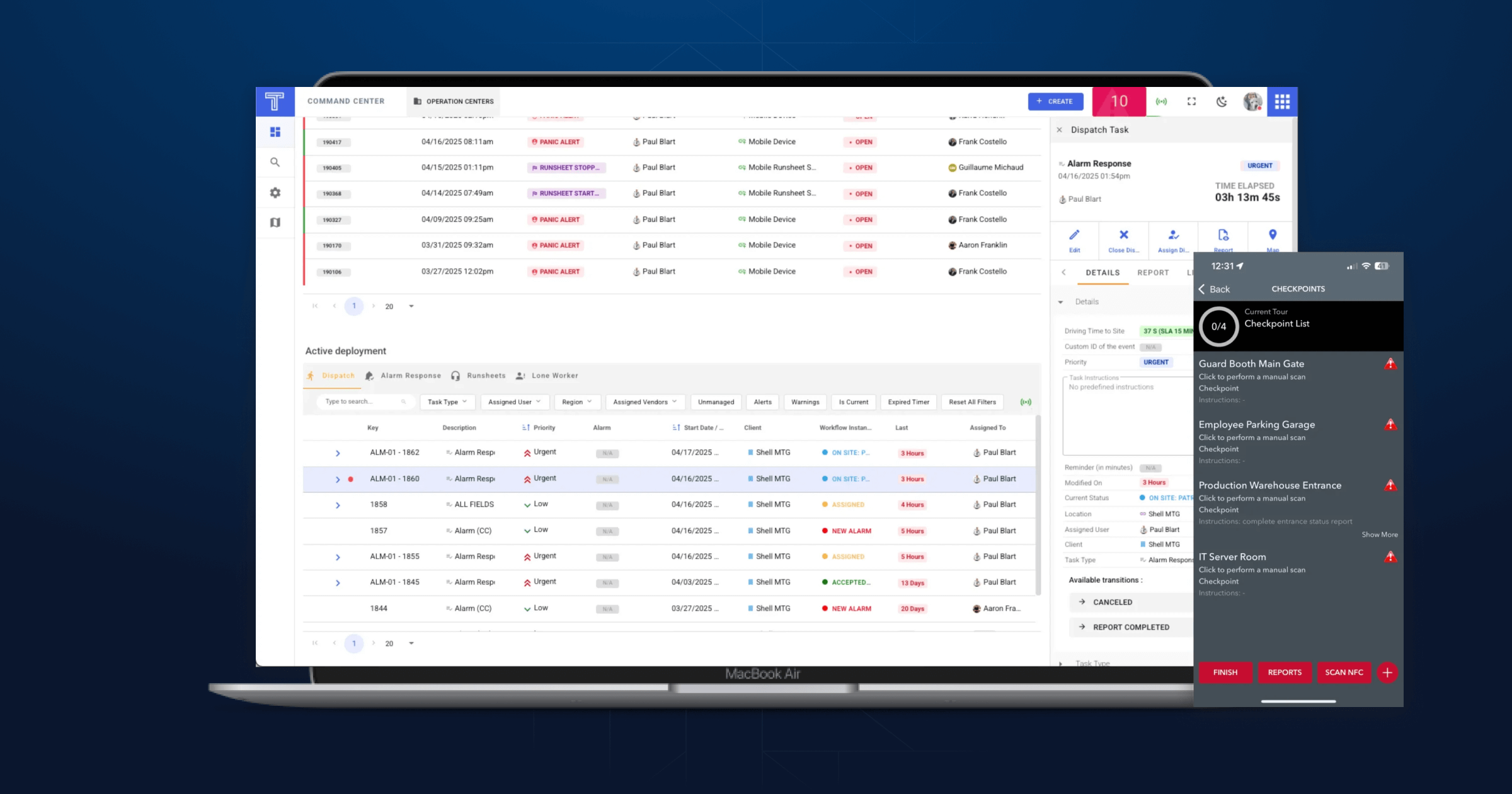
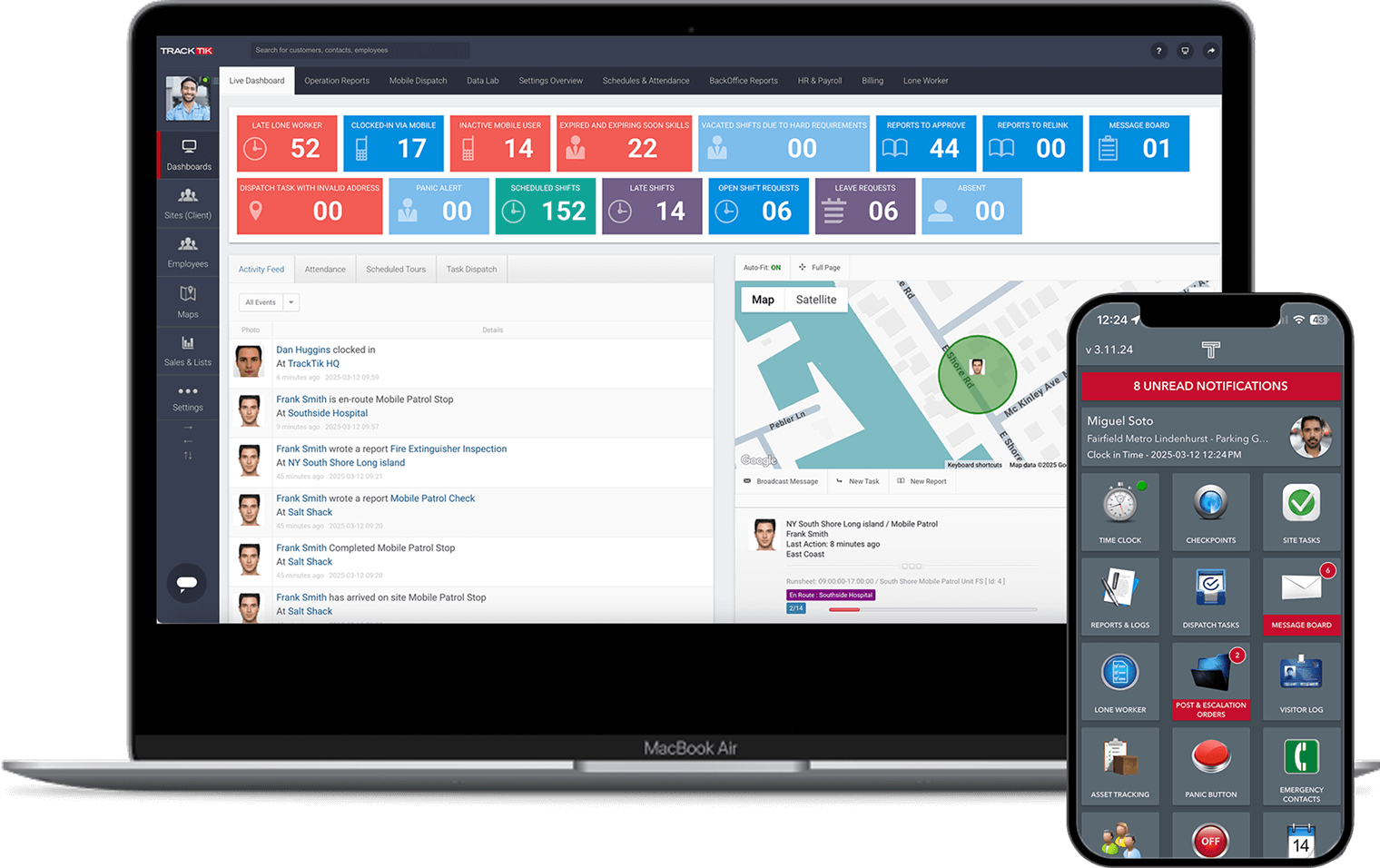
TrackTik: The Enterprise Leader
TrackTik remains unrivaled for enterprise security organizations. Its platform is purpose-built to solve enterprise-scale challenges.
Pros:
- Global Support: Native functionality for 55+ languages and local data residency ensures true coverage across continents and regulatory boundaries.
- Proactive Risk Management: Advanced analytics and standardized incident workflows empower teams to act before threats escalate.
- Automated Compliance: Robust audit trails, automatic policy enforcement, and consistent reporting support enterprise audit and industry requirements.
- Centralized Data Ownership & Control: Centralized management gives you visibility and ownership, with flexible local configurations for site-specific needs.
- Integration/API Ecosystem: Deep suite of integratable APIs provides “one pane of glass” for security operations, connecting seamlessly with your existing systems.
Cons:
- Slightly higher upfront investment—offset by a rapid ROI and operational efficiency.
- Full-suite feature set can require user education, which TrackTik addresses with extensive onboarding and support resources.
Bottom Line for Enterprise: TrackTik’s single-dashboard experience, true enterprise scalability, and modern API structure directly solve the pain points that matter most to security enterprises operating at scale.
Belfry
Belfry offers an all-in-one platform for scheduling, operations, billing, and payroll—suited mainly for small- to medium-sized guard companies.
Strengths:
- User-friendly scheduling and payroll.
- Automated timecards and billing improve operational efficiency.
- Mobile GPS tracking and incident reporting.
Enterprise Gaps:
- Lacks detailed compliance and multi-region regulatory tools.
- No indication of extensive global language support.
- Integrations are basic—APIs and deep system connectivity suited to complex SOCs are not a focus.
Connecteam
Connecteam is a flexible workforce management app, popular across various industries including security.
Strengths:
- Easy backend for mobile scheduling, communication, and task management.
- Modern interface and strong user adoption.
Enterprise Gaps:
- Lacks specialized security workflows such as detailed incident management, proactive threat analytics, and advanced audit capabilities.
- Integration ecosystem is focused on popular workplace tools, not comprehensive security operations.
- Global regulatory and multi-language features are limited compared to TrackTik.
24/7 Software
24/7 Software is recognized for venue and event operations management, putting emphasis on real-time communications and risk reduction.
Strengths:
- Effective for facility, event, and venue management.
- Good incident tracking and team communications.
Enterprise Gaps:
- Few global support features or compliance automation tools relevant for enterprise security teams dispersed across regions.
- Integration focus is limited, making unified command center functionality harder to achieve.
- Not tailored for consolidated enterprise-wide data control and reporting.
GuardsPro
GuardsPro targets guard tour and patrol operations, with modules for real-time tracking, reporting, and client communications.
Strengths:
- Mobile-friendly for on-field guard management.
- Tools for live GPS tracking, geofencing, and custom reports.
Enterprise Gaps:
- Lacks advanced incident analytics and enterprise-scale compliance features.
- API and systems integration capabilities for SOC environments are not emphasized.
- Limited resources for multilingual and multinational organizations.
Celayix
Celayix is known for employee scheduling and labor management across various sectors.
Strengths:
- Powerful scheduling automation and timesheet management.
- Focus on reducing overtime costs and compliance with basic regulations.
Enterprise Gaps:
- Security industry and enterprise-specific workflows are minimal.
- Integrations focus on HR and payroll, not incident management or advanced security operations.
- Global scalability (language, compliance, multi-site management) is not core.
OfficerReports
OfficerReports delivers a simplified platform for electronic reporting, GPS tracking, and scheduling.
Strengths:
- User-friendly for basic guard management and real-time reporting.
- Offers easy setup and adoption for small to mid-sized teams.
Enterprise Gaps:
- Not designed to withstand enterprise risk management, global deployment, or intense regulatory scrutiny.
- Integration tools are limited.
- Lacks advanced data ownership, audit, and API capabilities that enterprises demand.
Why TrackTik Leads for Enterprise Security
While each competitor addresses aspects of guard management, none deliver the full package required for enterprise security teams:
- TrackTik uniquely combines enterprise-grade global support, regulatory compliance, proactive risk management, and full data autonomy—addressing pain points that others cannot.
- Its robust API and integration suite means security operations centers can consolidate disparate apps and systems under one holistic view, streamlining processes and reducing risks at scale.
- With TrackTik, organizations gain a flexible, future-proof platform that evolves alongside their global operations.
Why API Connectivity Matters
Modern security operations centers rely on multiple specialized tools: video management systems, access control platforms, incident response software, and analytics tools. The ability to integrate these systems through robust API connections creates a unified operational view that transforms security effectiveness.
TrackTik’s comprehensive API architecture enables security teams to:
- Consolidate alerts and incidents from multiple systems into one dashboard
- Automate workforce deployment based on threat intelligence
- Maintain consistent reporting across all security applications
- Enable real-time coordination between different security tools
- Create comprehensive audit trails spanning all security operations
This “one pane of glass” approach eliminates the inefficiencies and blind spots created when security teams must monitor multiple disconnected systems.
The Clear Winner for Enterprise Security: TrackTik
While multiple workforce management platforms serve general business needs, enterprise security teams require specialized capabilities that only TrackTik provides comprehensively. The platform’s combination of global scale support, advanced integration capabilities, and security-specific features makes it the clear choice for enterprise operations.
The ability to consolidate multiple security applications into one operational view transforms how enterprise security teams work. Instead of managing disparate systems, security leaders gain complete visibility and control through TrackTik’s unified platform.
For enterprise security teams serious about scaling their operations while maintaining the highest standards of compliance and effectiveness, TrackTik provides the comprehensive solution needed to succeed in today’s complex threat environment.
Want to make an informed decision about your next security workforce management platform?
Our comprehensive buyer’s guide breaks down exactly what to look for, key questions to ask vendors, and how to evaluate solutions against your specific enterprise requirements. Download the complete buyer’s guide to ensure you choose the right platform the first time.

Want to make an informed decision about your next security workforce management platform?
Frequently Asked Questions
Want to understand all the factors driving guard turnover?
Download our comprehensive “Ultimate Guide to Retaining Your Security Guards” for actionable insights.